LLMs’ Data-Control Path Insecurity
We need to think carefully about using LLMs in potentially adversarial situations . . . like on the Internet.
Vendor Software Solutions in a Cloudy World
Assessing on-premise deployments vs. cloud-hosted solutions.
Do Know Harm: Considering the Ethics of Online Community Research
Strategies for engaging in more ethical research with online communities.
On the Difference between Security and Safety
Safe networking requires us to be skeptical of messages that try to stampede us into action without enough forethought.
What We're Reading
Opinion
Views on issues of broad interest to the computing community
BLOG@CACM
Thought leaders discuss relevant computing topics
Explore the latest issue
Table of Contents
Video
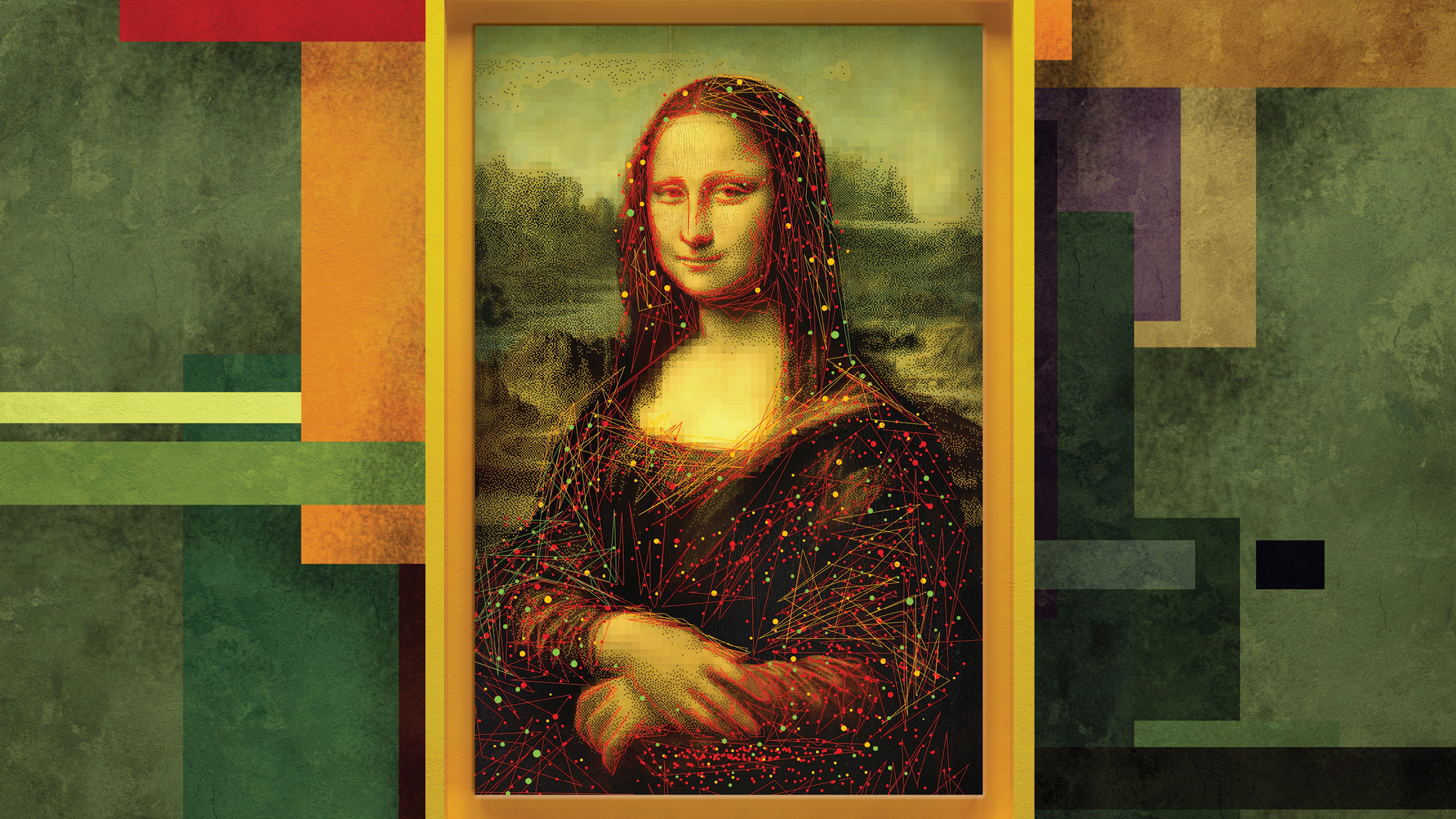
Computer Vision, ML, and AI in the Study of Fine Art
Immense challenges and opportunities remain for the application of AI in the study of fine-art paintings and drawings.
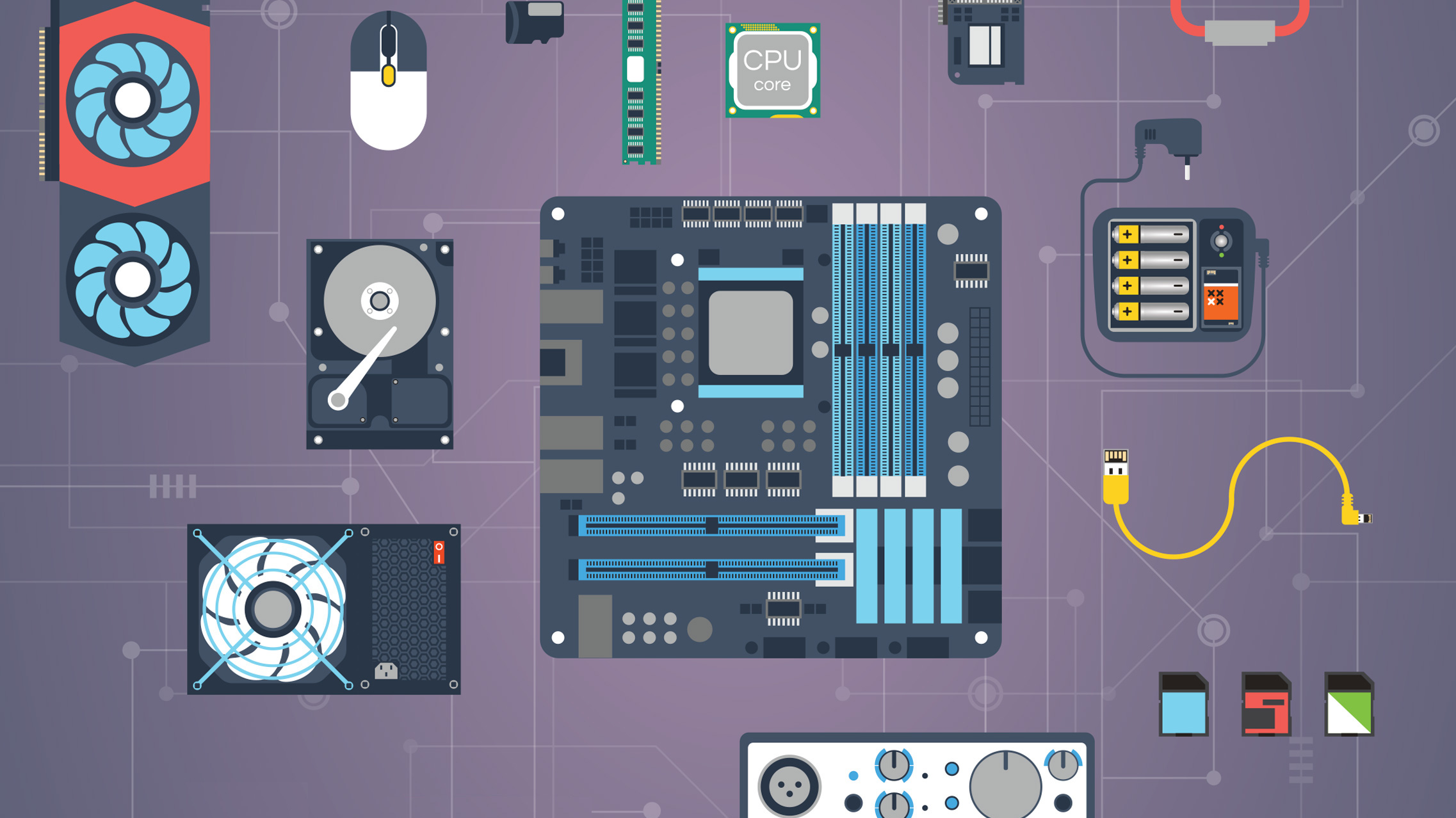
Nand to Tetris: Building a Modern Computer System from First Principles
CS course walks students through a step-by-step construction of a complete, general-purpose computer system—hardware and software—in one semester.
The Science of Detecting LLM-Generated Text
A technical introduction to LLM-generated text detection methods.
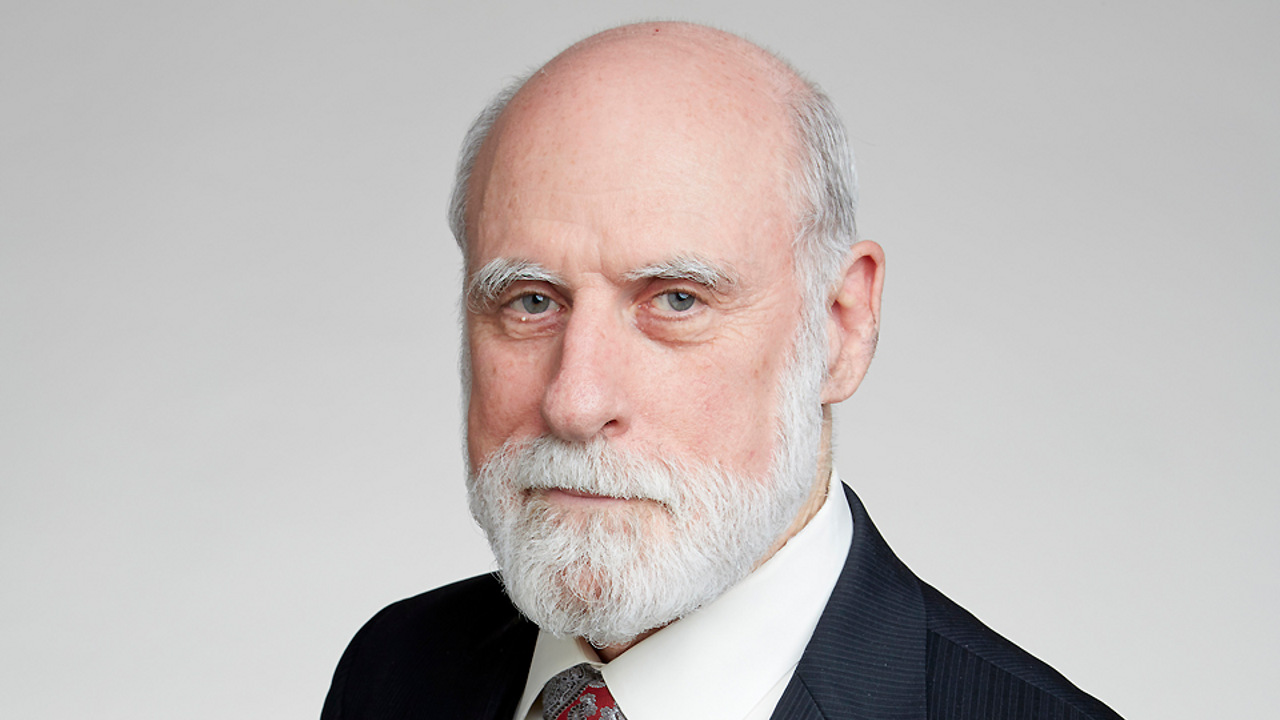
Have technical limitations of the Internet architecture contributed to the rise of doom scrolling on social media?]
Shape the Future of Computing
ACM encourages its members to take a direct hand in shaping the future of the association. There are more ways than ever to get involved.
Get InvolvedCommunications of the ACM (CACM) is now a fully Open Access publication.
By opening CACM to the world, we hope to increase engagement among the broader computer science community and encourage non-members to discover the rich resources ACM has to offer.
Learn More